Executive Summary
A professional services organisation discovered that fraudulent payment change requests had been sent to multiple clients from an employee's legitimate Microsoft 365 mailbox.
The emails passed all authentication checks and appeared indistinguishable from genuine communications. Clients had been instructed to redirect payments to attacker-controlled bank accounts.
Because the fraudulent messages originated from a real internal mailbox, the organisation needed to determine how the attacker had gained access and whether additional accounts had been compromised.
CyberQuell was engaged to investigate the incident, identify the root cause of the compromise, and recommend remediation measures.
Following a comprehensive forensic review spanning multiple incidents over a four-month period, CyberQuell determined that a sophisticated threat actor had maintained persistent access to a key employee's mailbox through session token theft and malicious Outlook rules. The attacker had survived multiple remediation attempts.
CyberQuell's investigation enabled complete threat eradication and implementation of hardened security controls. No financial loss occurred.
Client Environment
The organisation operates a professional services business with approximately 50 employees across multiple locations.
Operational workflows include:
- client invoicing and accounts receivable management
- ACH and wire payment processing
- coordination with external clients and vendors
- Microsoft 365 email for all business communication
The Accounts Payable function was managed by a single bookkeeper with direct access to banking systems and regular client payment interactions.
The organisation used Microsoft 365 with basic MFA enabled through the Microsoft Authenticator app. Legacy authentication protocols remained active for compatibility with older applications.
Incident Timeline
Incident Trigger
The incident was detected when a client contacted the organisation to verify an unusual ACH payment change request.
The client had received an email from the bookkeeper's legitimate email address requesting updated payment instructions. The email appeared authentic and passed all standard email authentication checks.
When the finance team reviewed the request, they confirmed that no such communication had been authorised.
This raised immediate concerns that the employee's mailbox had been compromised and that additional clients may have received similar fraudulent requests.
Security Concern
The situation was critical for several reasons.
The fraudulent emails originated from a real Microsoft 365 mailbox, not an external impersonation. All email authentication mechanisms (SPF, DKIM, DMARC) confirmed the messages as legitimate.
Upon investigation, malicious Outlook rules were discovered that automatically redirected client replies to a hidden folder, preventing the employee from seeing responses to the fraudulent requests.
Most concerning, a previous security incident three months earlier had prompted password resets and session revocations. Despite these measures, the attacker had maintained access to the mailbox.
The organisation needed to determine how the attacker had gained initial access, how they had maintained persistence despite remediation, and whether additional accounts or systems had been compromised.
CyberQuell was engaged to investigate.
Attack Anatomy
CyberQuell's investigation revealed a sophisticated, multi-phase campaign executed by a single threat actor over at least four months.
Phase 1 - Initial Access and Reconnaissance
The attacker gained access to the bookkeeper's mailbox through a session token theft technique that bypassed standard MFA protections. The attacker monitored email conversations to identify client relationships and payment patterns.
Phase 2 - Financial Fraud Attempts
Using the compromised mailbox, the attacker sent fraudulent ACH payment change requests to multiple clients. The attacker created Outlook rules to intercept and hide client replies, preventing detection.
Phase 3 - Parallel Infrastructure
The attacker also registered typosquatted domains designed to impersonate the organisation. These domains were used in separate BEC attempts and to create fraudulent cloud service accounts for phishing campaigns.
Phase 4 - Persistence
The attacker maintained access through multiple remediation cycles, likely through a malicious OAuth application with delegated mailbox permissions that survived password resets.
Technical Root Cause Breakdown
CyberQuell Investigation
CyberQuell conducted a structured forensic investigation to determine the scope of the compromise and identify the root cause of persistent access.
Phase 1 - Incident Triage
Initial steps included:
- confirming scope of mailbox compromise
- identifying affected clients and communications
- preserving email headers and authentication logs
- documenting attacker infrastructure
Phase 2 - Microsoft 365 Forensic Review
CyberQuell performed a detailed analysis of Microsoft 365 security telemetry, including:
- Azure AD sign-in logs and authentication patterns
- mailbox audit logs and email forwarding configurations
- OAuth application permissions and delegated access
- Outlook rules across affected mailboxes
- email header forensics for authentication validation
Phase 3 - Attribution and Timeline Reconstruction
CyberQuell correlated evidence across multiple incidents to establish a unified attack timeline. The investigation confirmed that all incidents were connected to a single threat actor who had maintained persistent access for at least four months.
Phase 4 - Validation
Following remediation actions, CyberQuell validated that:
- all unauthorised access had been terminated
- malicious OAuth applications had been revoked
- malicious Outlook rules had been removed
- no additional accounts had been compromised
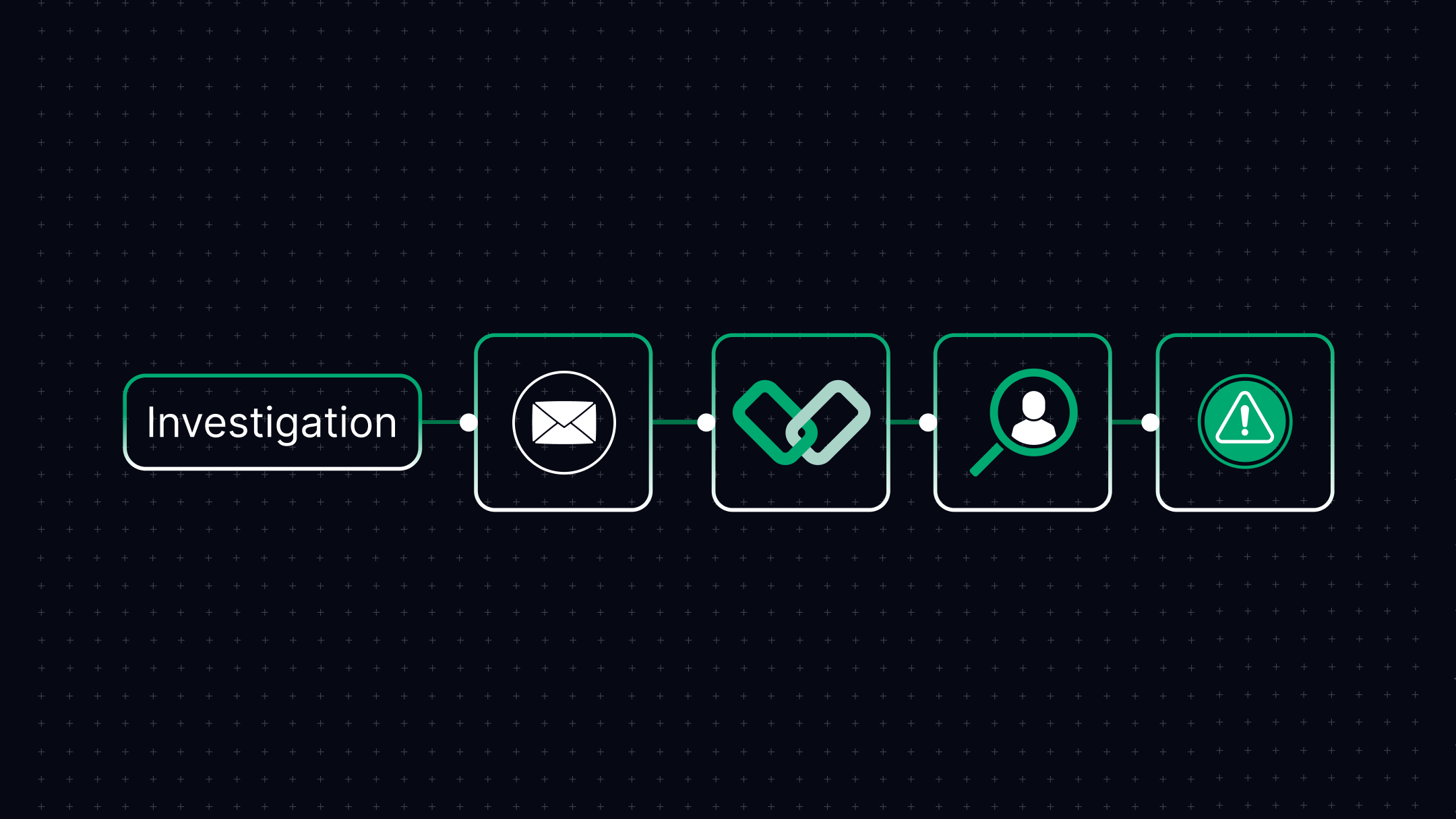
How CyberQuell Investigated This Multi-Phase Attack
A deep forensic investigation to trace attacker activity, identify persistence mechanisms, and reconstruct a four-month compromise timeline across multiple incidents.
Key Findings
The investigation confirmed that a sophisticated threat actor had compromised a key employee's Microsoft 365 mailbox and maintained access for over four months.
Key findings included:
- The attacker used session token theft to bypass MFA protections
- Malicious Outlook rules were used to hide fraudulent activity
- OAuth application persistence allowed access to survive password resets
- Two typosquatted domains were registered to support the campaign
- Multiple clients were targeted for payment diversion fraud
- Employee vigilance prevented all financial losses
Remediation and Hardening
Following the investigation, CyberQuell implemented comprehensive remediation measures.
- Revoking all OAuth application permissions
- Removing malicious Outlook rules
- Disabling legacy authentication protocols
- Blocking typosquatted domains
- Notifying affected clients
- Deploying phishing-resistant MFA (FIDO2 hardware keys)
- Implementing Conditional Access policies
- Enabling Microsoft Defender for Office 365
- Configuring automated detection rules for suspicious activity
- Implementing out-of-band verification for payment changes
- Establishing dual-authorisation for wire transfers
- Deploying regular phishing simulation training
Business Impact
CyberQuell's investigation provided immediate clarity during a high-risk security event.
The organisation was able to:
- confirm the root cause of persistent mailbox compromise
- achieve complete threat eradication
- prevent all financial losses through timely detection
- implement hardened security controls
- document the incident for compliance and insurance purposes
Key Lessons
Business Email Compromise attacks increasingly target legitimate mailbox access rather than external impersonation.
Session token theft can bypass standard MFA protections without triggering authentication alerts.
OAuth applications can maintain persistent access even after password resets and session revocations.
Outlook rules provide attackers with a mechanism to hide fraudulent activity from mailbox owners.
Payment verification procedures remain critical as a final line of defence against financial fraud.
Regular security audits of application permissions and mailbox configurations can detect compromise indicators before fraud occurs.